Malware Removal
A malware can be any malicious software or file that infects a digital device. Hackers make use of malware to steal personal details and credentials, or to lock you out of your computer. The word “malware” is the short form of “malicious software”, which can be harmful or annoying that can secretly access the device of a user without his or her knowledge.
Malware programs can steal, delete, or encrypt sensitive data of users as well as hijack or alter the core functions and monitor the computer activities of the user without permission. These programs can cause simple annoyances (like pop-ups) to serious invasion and damage such as stealing sensitive data and passwords or infecting other computers connected to the network. There are also some malware programs that are designed to collect data about your browsing habits and send them to advertisers and other third party agencies without your knowledge.
Types of Malware
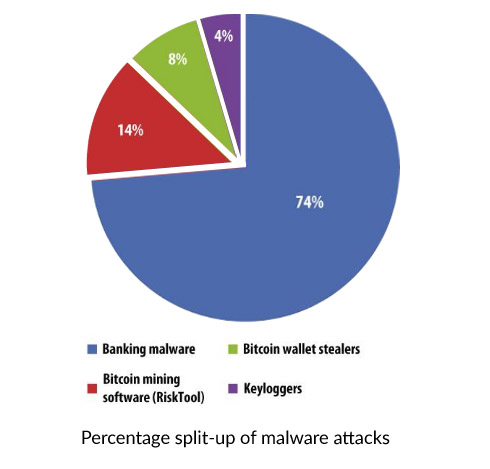
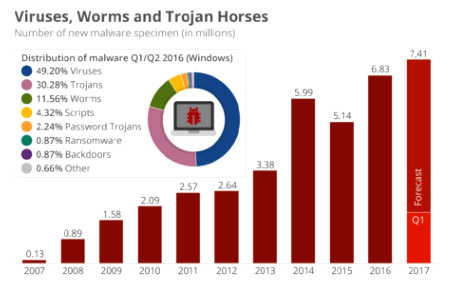
Malware programs can be classified into different types based on their unique characteristics. Statistics show that malware attacks are on the rise every year and that banking malware attack is the most common type. The below graph will give you an idea of the extent of banking malware attacks.
Malware programs can be classified into different types based on the mode of infection and the type of attack. The various types of malware programs are explained below.
Basic types of malware
Adware
Adware is the short form for advertising-supported software and is a type of malware that delivers ads automatically. Examples for adware can be the advertisements displayed by software programs and pop-up ads on various websites. Usually, applications and software offer free versions that are bundled with adware programs. Most of the adware programs are made or sponsored by advertisers, and usually, serve as tools to generate revenue.
Rootkit
Rootkits are malicious software that is designed to remotely control or access a computer without being detected by antivirus programs or by users. After a rootkit infects your computer, the party behind the infection will be able to remotely access and steal data, execute files, make changes to system configurations, install more concealed malware, or remotely control the computer. Owing to the stealthy operation of rootkits, it is extremely difficult to detect, prevent, or remove them.
Bug
In software terms, a bug is a flaw that leads to an undesirable outcome. Usually, these flaws are caused by human error and can exist in the compiler or source code of a program. Minor bugs may not alter the behavior of a program largely and can go unnoticed for long periods. However, major bugs can lead to freezing or crashing of computers. The most severe types of bugs are the security bugs as they can allow attackers to override user privileges, bypass authentication, or steal information.
Ransomware
This type of malware holds the computer system captive and demands ransom from the users. Ransomware will restrict access to the computer system either by locking down the system or by encrypting the files stored in the computer and will display messages that force the user to pay for the removal of restrictions to get back the access. This type of malware can affect your computer through downloaded files or through network vulnerabilities.
Spyware
This type of malware usually spies on the computer activities of the user without their knowledge. The spying capabilities of the malware can include data harvesting, activity monitoring, and keystroke collection. Spyware programs can also have additional capabilities like altering the security settings of browsers and software to interfere with the network connection. Spyware usually spread by bundling with legitimate software, or by exploiting vulnerabilities in software.
Virus
Viruses are dangerous forms of malware that can replicate itself and spreads to other computers. The full form of the virus is Vital Information Resources Under Siege. Virus programs attach themselves to different programs and execute their code when the user launches the infected program. They can also spread via documents, script files, and cross-site scripting vulnerabilities. Viruses can harm the host computer, steal data and money, render ads, and much more.
Trojan
A Trojan malware disguises itself as a normal program or a file and trick users to download and install it. This type of malware can offer the third party remote access to the infected PC. After getting access to the computer, the attacker can steal user credentials and financial details, modify stored files, install more malware, as well as monitor user activities.
Worm
Worms are one of the most common types of malware and spread over the networks making use of vulnerabilities in the operating system. Typically, worms cause harm to the networks by overloading the servers and eating up the bandwidth. They can also include “payloads” to damage host computers. Payloads are code snippets that are intended to do specific actions on the affected computers beyond just spreading the worm.
Symptoms of Malware Infection
The different types of malware infect and spread through different ways, but many of them show similar symptoms. A slow computer can be a sign of a malware infection. Some of the other signs can be frequent crashes, annoying pop-ups, and spam. If your doubt that your computer is infected with malware, look for the following symptoms.
- Slow computer or slow browsing speeds
- Increase in CPU usage
- Unable to connect to networks
- Frequent crashing or freezing
- Deleted or modified files
- Appearance of strange icons, programs, or files
- Programs executing, reconfiguring, and closing themselves
- Messages and emails being sent automatically without your knowledge
- Strange computer behavior
How to Remove Malware
Malware programs can cause much annoyance to users and can be persistent. You can download many malware removal tools online, but many of them are not effective in removing the malware programs completely from your PC. Even worse, some of the programs may install more malware to the computer. Therefore, the best way is to contact our malware removal team.
Why Choose Us
Our expert technicians can efficiently remove malware from your PC or Mac, by remote access. Installing anti malware programs cannot ensure complete removal, whereas, our technicians will be able to remove the malware infection entirely from your computer. The services offered by our technicians include:
- In depth scan of your computer
- Installation and upgrading of anti malware software
- Troubleshooting malware issues
- Removal of malware infections
- Optimizing the computer performance and speed
With our 24/7 support via phone, chat, or email, and through the secure remote sessions, we can ensure complete malware removal from your computer. Contact us any time to enjoy the best malware removal service.